
LateralAccessDevice
takes you back to before the Internet
How It Works | Download LAD | Support | LAD Security | Features & Uses | Resources | Members | User Guide
Sample Configurations for Professional Users: Debugging Network Connectivity Functions with LAD's Passthrough Packet CaptureAre you a software developer, web developer or web-software developer? You likely spend a lot of time dealing with internet or network connectivity and related issues. In those situations, it is quite handy to have LAD available with four network interfaces to be able to work and debug all through one device, without the need for awkward setups to be able to get the info you need for debugging. In the simplest configuration (and you likely don't need anything but the simplest), you would have LAD's port 0 connected to the Internet, port 1 connected to your computer and ports 2 and 3 for capturing the packets of the device(s) or application(s) whose communications or protocol implementations you need to debug, be they web services, network appliances, SaaS or what have you. 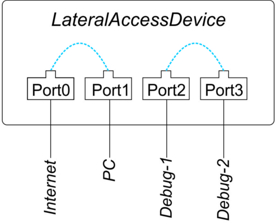
in the above illustrated scenario ports 2 and 3 are configured as passthrough ports to each other (and to each other only). In this fashion, on its own LAD captures all of the traffic sent between those two points (that is the two devices connected to ports 2 and 3 that you are debugging), undetectably and without alteration. You even get highly accurate timestamping. Even better, you can easily get the data from the debug ports onto your working machine connected to port 1, without interfering in any way with the communications on ports 2 and 3. Nor will the debug communications interfere with your work computer or its connectivity to Internet or wider network. In addition to the raw packet data invaluable for debugging, captured in full and timestamped, LAD delivers automated reports on MAC address usage (which can be extremely convenient). So, with LAD, in one box you get wirespeed pass-through packet capture that cannot be bypassed, with GPS-synchronized accuracy for timestamping of the packets and reports, with no additional equipment. Working in a small office or on your own? Expand LAD to six or eight or more ports and you still get all of the above: two dedicated ports with passthrough packet capture for debugging with additional connections available for the rest of your network, all without interfering with your capture of your debug work. Passthrough packet capture is very much the hallmark of commercial-grade packet capture systems because it is neither detectable nor bypassable. |